The information in this article is meant for educational purposes only. There should be no attempt to practice the discussed concepts in this article on unauthorized systems. Please use this knowledge responsibly and ethically.
Locking PDFs is a really good security practice. Especially if the said PDF (Portable Document Format) contains delicate information. In this article, we’re going to see how to crack locked PDFs.
I know you must be wondering. We’re the good guys and this sounds like an evil task :) so why are we doing it? Sometimes, in order to protect against something in the best possible way, we need to know how it actually works first. Some people think it’s all bluffs when they hear that hackers can crack their passwords so with illustrations like what I’m about to show you, they see the possibilities and can now make more informed decisions.
Also, security practitioners need these skillsets. After all, knowledge is knowledge. What distinguishes us is how we use it. Imagine working as a digital forensic analyst at an organization that investigates cybercrime. During your course of investigating malicious actors (ethically and legally), if you stumble upon locked PDFs, you should be able to attempt cracking them, as these PDFs may contain valuable information that may aid your Investigation.
A skillset like this, can also help us in situations where we forget the password we set. We can attempt to crack it. Even though I expect you to set an “uncrackable” password.
In this article, we’ll use a program called “PDFCrack” for password cracking. We’re going to install it on our hacking OS (Operating system), Kali Linux. Kali is what I use. You might be on a different OS, that’s fine. The process of installing it on Kali, is quite similar for all other Unix based OS’s. PDFCrack works on other OS’s too. Feel free to do research on how to get it on your OS. However, in this article, I’m going to show you how to get it and work with it on Kali as this is the preferred hacking OS in the security community.
PDFCrack is a command-line tool used for recovering the passwords of password-protected PDF files. It operates by attempting to guess or crack the password through a process called brute-forcing. Brute-forcing involves systematically trying all possible password combinations until the correct one is found. Been talking too much, let’s get into it!
First, we install the program (if you don’t have it already). To do this, open up your terminal and run:
$ sudo apt-get update
$ sudo apt-get install pdfcrackYou should run these commands one at a time, in that order. The update command is used in Debian-based Linux distributions, including Ubuntu and Kali Linux, to update the package lists for available software packages from the repositories configured on your system. The install command basically installs the program for us. If you already have the program, you’ll be notified on your terminal. Also, make sure to have an internet connection.
I already have it installed. If you don’t, your screen would be different (installing it).
A very important thing to note is that whenever we install a program and don’t know how it works, we can use the help flag to gain more insight into its functionality. Run this to see how the program works.
$ pdfcrack --helpNow, we have the program. The cracking process can begin.
In the above image, we can see three PDFs. We also see that they all have lock icons. This indicates that these PDFs are password protected. We’ll attempt to crack them!
Upon trying to access the test.pdf, a prompt is asking me to enter the password.
Now, to start cracking the PDFs, we need to navigate to the directory where the PDFs are located (via the terminal). I’m going to be showing you the cracking process in different scenarios.
Scenario 1
In this scenario, we assume that we have seen the user enter their password before. We don’t really know what it is, but we know it’s all digits. So, while in the directory where the target PDF (test.pdf) is, we type in the command:
$ pdfcrack -c 0123456789 -f test.pdfpdfcrack is the name of the program that does the job (as discussed earlier).
The c flag specifies the character set we want the program to work with. In our case, we’re telling it to test only digits (0–9). This is because we have seen the target enter the password, and even though we don’t know the password, we know it’s only numbers.
The -f flag basically tells the program that this is the file we want to crack.
Password found!
And just like that, we were able to get the password. The takeaway from this scenario is that if your password is all-digits, you’re as good as done! Not just for a PDF, if your Wi-Fi or any account password is all-digits (when you have the option of mixing different characters), you’re as good as done. It’s very easy to crack all-digit passwords because there are less combinations to try (0–9). And with today’s computing power, in seconds your password can be easily obtained.
Also, this method of trying out for only digits is not limited to only when we see the target entering their password. Even if you’re clueless about the password, try it because trust me a lot of people still use all-digit passwords. Especially for things like this — a PDF.
Scenario 2
Unlike the first scenario where we had a bit of insight to what this password could be, in this scenario, we have zero clues to what the password could be. This is a more realistic scenario. In this scenario, we capitalize on the target’s laziness or ignorance. A lot of people often use common passwords because they don’t like “stress” or they don’t just know the dangers involved. So they opt for common (weak) passwords. These passwords include password, Passw0rd, P@55w0rd, 123456789, access, letmein, welcome, qwerty, admin, iloveyou, abc123, password123, and names. If your password is here or close to something here, well...
Anyway, attackers know these common passwords. So they put all these passwords together in a single file (wordlist) and try every single one of them. Not manually of course, just as we saw in the first scenario, there are a lot of programs that do these automatically — in a matter of seconds. Also, sometimes our passwords might actually be strong but if it happens to appear in a data breach, this password can be added to the word-list to amplify the probability of success of the attacks. This is why it is not a good practice to use the same password across different accounts and assets.
So, to the cracking!
The procedure is quite similar to the first scenario. The difference is that in this scenario, we specify a wordlist. The program is going to try every password in this wordlist until it finds the right password (if it’s there).
Kali comes with a few wordlists. These word-lists are very efficient because they carry a wide range of passwords, covering different character combinations. In this example, I’m going to use the rockyou.txt word-list, it can be found in /usr/share/wordlists. If you’re not on Kali, you can still download the wordlist here. On kali, the wordlist may be zipped. To unzip it, run:
$ gunzip rockyou.txt.gzTo see the content of this file:
$ cat rockyou.txtNow that we know the wordlist we want to use, we can pass it to our pdfcrack program
$ pdfcrack -w /usr/share/wordlists/rockyou.txt -f test3.pdfThe w flag indicates the wordlist we want to use. Make sure to specify the full path of the wordlist if you aren’t in that directory.
Again, password found!
The program was able to crack the PDF because the target’s password was in the wordlist. The success of this attack depends on the accuracy of the wordlist. This is why you are encouraged not to use common or guessable passwords.
We know you love your pet, there are other ways of showing love to your pets. It’s not by using their names as passwords. Whenever you’re prompted to set a password, make sure to use different characters. Uppercase, Lowercase, numbers, special characters and length. Combine them all! And resist the urge to use the same password across multiple accounts.
If you’re scared that you may forget, password managers are your friends! Also feel free to try out other wordlists (on Kali and online). A simple google search would do.
Scenario 3
Just like in scenario 1, if we manage to see some characters in a target’s password, we can create our own custom wordlist with certain patterns. Say for example, we see the target input “A” as the first character and “2” as the last, and we know the character length of the password, even if we don’t know other characters, we can be able to create our own custom wordlist with this info. This would increase the effectiveness of the wordlist as it’s going to contain only very closely related combinations. This amplifies the chances of success of the attack.
We can create a custom wordlist with a tool like crunch. This is the toolI prefer to use. However, discussing how to use crunch is a topic of its own so I won’t be talking about it now. Probably in a future tutorial. For now, you can learn a bit about crunch here. You can also use the --help flag to see how it works.
Additional Notes
If you want to lock a PDF, it is achievable with a tool like pdftk.
On Linux, install it by running:
$ sudo apt-get install pdftkYou can also lock a PDF using our very own PDF Locker.
After installing it, navigate to the directory containing the file you want to lock and run the following command to lock a desired PDF:
$ pdftk [name of file to be locked] output [any desired name for the locked file] user_pw PROMPTE.g
$ pdftk test1.pdf output locked_test1.pdf user_pw PROMPTThe user_pw allows us to set the password for the file. Passing PROMPT after this parameter is like a secure way of entering our password. Afterwards, hit enter and notice you now have a new file in the directory.
It will be named according to the name we give in the output parameter and can only be accessed with the password we set. Please use secure passwords. Also, locking PDFs using pdftk is not limited to Kali alone. Feel free to do research on how to use it on other OSs.
So, we’ve seen it. Locking our files is a really excellent security measure, but it’s equivalent to a leaking bucket if we go ahead and use weak (useless) passwords.
I hope you enjoyed this one.
Till next time!
Related Tutorials
Step-by-Step Metasploitable2 Exploitation Guide f…
A complete, beginner-friendly penetration testing tutorial for cybersecurity st…
Read Tutorial
Preparing for Your Next Web Pentest
A practical guide to pre-attack reconnaissance: setting engagement rules, Googl…
Read Tutorial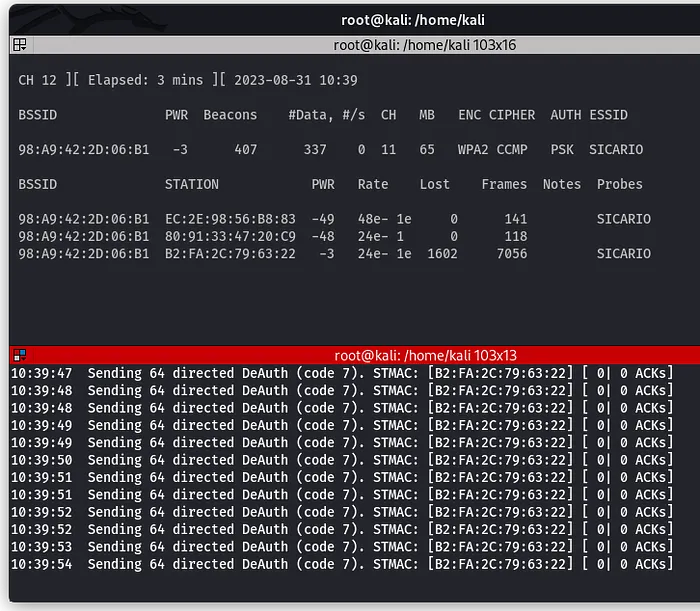
How to Perform a Wi-Fi Deauthentication Attack
Learn how Wi-Fi deauthentication attacks work and how targets can be forcibly d…
Read Tutorial

Discussion (0 comments)
Join the Discussion
No comments yet
Be the first to share your thoughts on this tutorial!